Nmap cheat sheet: From discovery to exploits, Part 3: Gathering additional information about host and network | Infosec Resources

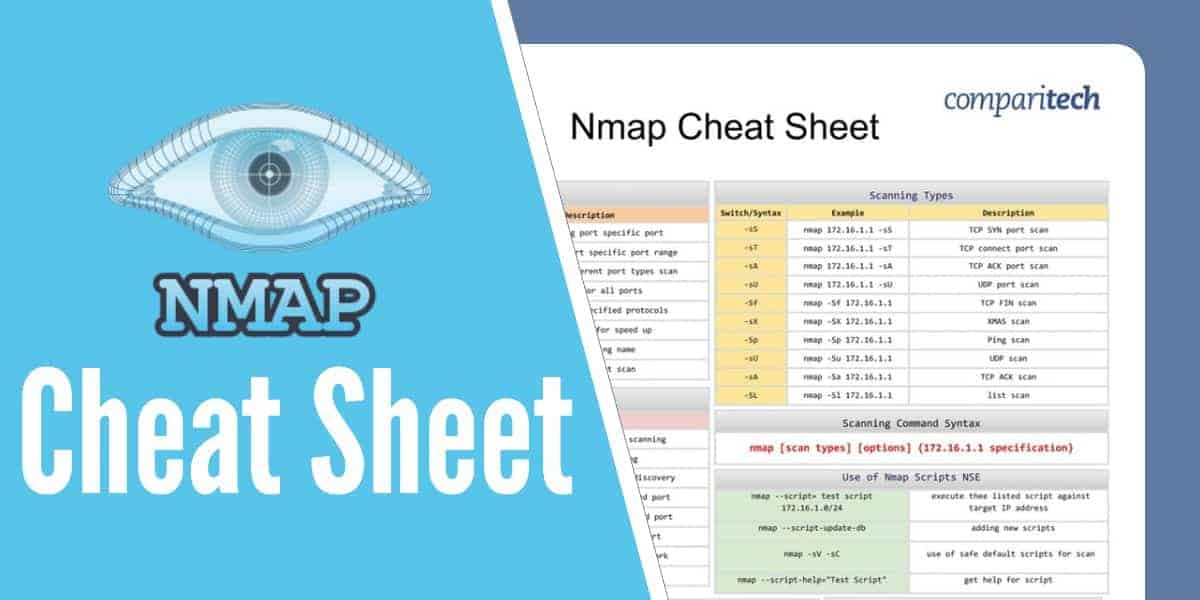
StationX on Twitter: "The Ultimate Nmap Cheat Sheet #hacking #nmap #infosec https://t.co/zIoUoGzTgV https://t.co/EEjMeVN5ry" / Twitter

Nmap cheat sheet: From discovery to exploits, part 2: Advance port scanning with Nmap and custom idle scan | Infosec Resources